Internet Architecture and Systems

Research Staff
-

Professor
Kazutoshi FUJIKAWA -

Professor
Ismail ARAI -

Affiliate Associate Professor
Shigeru KASHIHARA -

Affiliate Associate Professor
Akira YUTANI -

Affiliate Associate Professor
Masatoshi KAKIUCHII -

Assistant Professor
Arata ENDO -

Assistant Professor
Kibrom Desta ARAYA
| inet-info@is.naist.jp | |
| To the site | http://inet-lab.naist.jp/en/ |
Research Areas
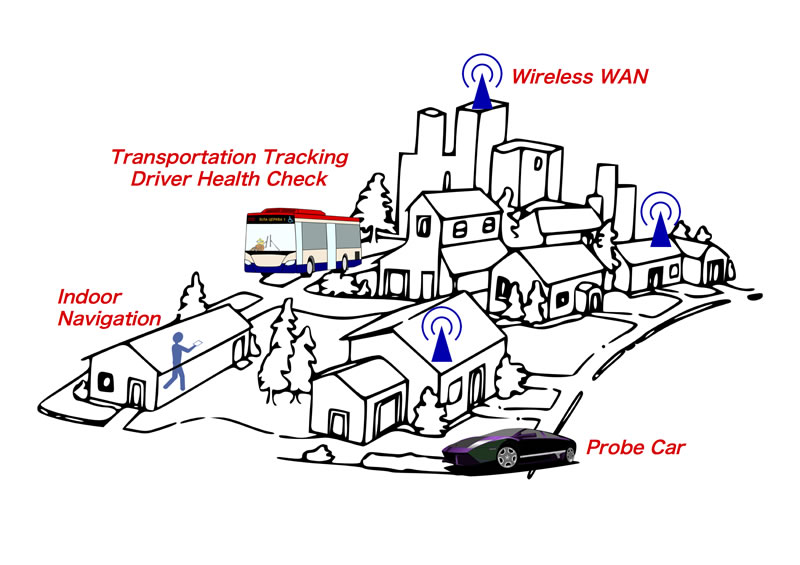
Fig.1 Pervasive Computing / Ubiquitous Computing
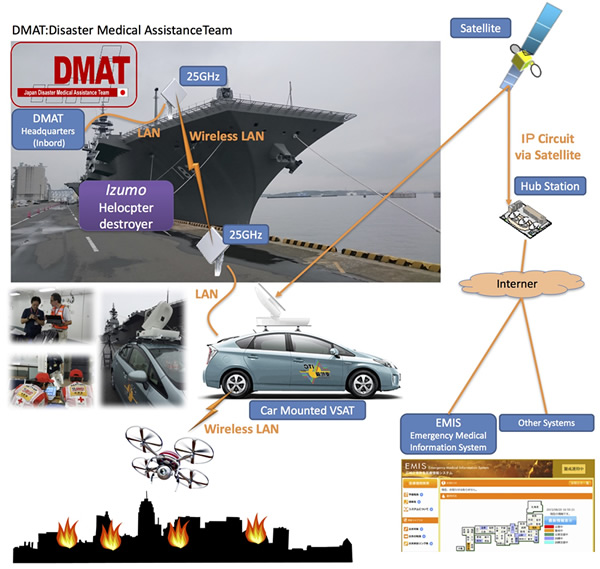
Fig.2 Disaster relief computing / networking

Fig.3 Operations technology for data center and network

Fig.4 Cyber Security
Pervasive Computing / Ubiquitous Computing
In an environment which everything in real space is connected to the network (IoT, M2M environment) the information system analyzes and understands the sensor data then controls remote devices and presents useful decision-making information.
- Public transportation big data analysis (ex. driving analysis)
- Indoor localization utilizing environment sensors and smartphone mounted sensors together
- Edge/Fog computing (Optimization of computing resource allocation for smart cities)
Disaster relief computing / networking
In large-scale disasters such as communication infrastructure being cut off, the use of satellite communication system becomes extremely important. We are conducting R & D on communication methods that make maximum use of limited resources of low bandwidth / high latency satellite lines. At the time of the initial disaster occurrence, on-site staff need to devote themselves to disaster response, and we are also discussing ways to provide the environment where terminals can be normally used as they are.
Operations technology for data centesr and networks
We are working on the operations technologies for data centers that is developing with higher performance and higher density with the spread of cloud computing. In particular, we are studying on the following technologies on data management for online storage for storing and sharing data in networks, resource management and operations support for cloud service infrastructure and routing control for network traffic.
- Network storage system adaptation to data properties (object storage, distributed storage, access control)
- Technologies for virtual machine placement, data placement, traffic control and operations support considering energy saving and load balancing
- Next-generation traffic engineering for safe and effective data transport (IPv6 site multihoming, network auto configuration)
- Technologies for IPv4-IPv6 transition and IPv6 deployment
Cyber Security
Devices which is connected to the Internet are always threatened with malware and DoS attacks.
With the spreading of IoT or M2M technologies, it is important to care about the vulnerabilities of various devices such as automobiles, robots, sensor nodes, etc. as well as servers and PCs.
- DoS attack of industrial network and devices
- Car security
- Malware analysys
High-Performance Computing (HPC)
Today’s supercomputers often adopt a cluster architecture, which is composed of many computers connected to a network, to provide massive computing performance. For improving computing performance on these systems, not only the computing performance of a computer but also network performance are important. We tackle a problem derived from the mutual interference between the network traffic of data movement and the one of inter-node communication.
Key Features
In our laboratory, students can study a variety of topics concerned with computer networks, from the network layer to the application layer. The strength of our laboratory is that students have opportunities to perform their research using actual computer network environments because all faculty members are engaged in the Information Initiative Center (ITC) of NAIST. Additionally, in some cases we develop devices to create appropriate research environments. Our laboratory welcomes students of all levels of expertise, providing seminars on basic theoretical and practical studies as well as advanced areas.